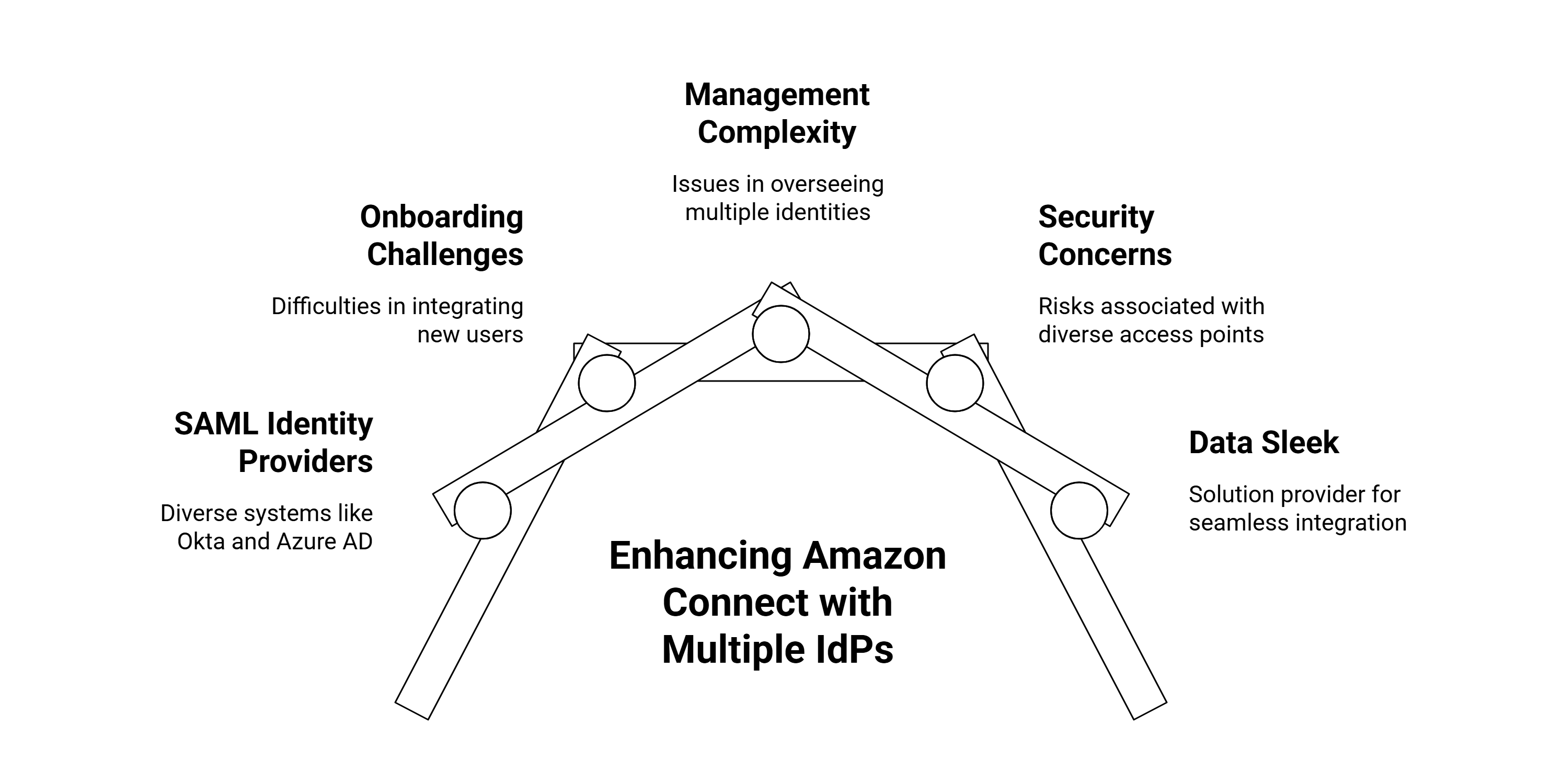
In today’s fast-moving digital landscape, enterprises rarely rely on a single identity system. Different departments, subsidiaries, or partner organizations often use different SAML Identity Providers (IdPs)—ranging from Okta and Azure AD to Ping Identity and Google Workspace.
Traditionally, contact centers faced a limitation: each Amazon Connect instance could only integrate with one IdP, which created friction in onboarding, managing, and securing diverse workforces.
Amazon Connect offers flexibility to integrate multiple SAML identity providers within a single instance. This means businesses can centralize customer engagement while maintaining secure, seamless access for agents, supervisors, and third-party collaborators—without the headaches of running separate environments.
This blog explores why this matters, the challenges companies face, how to implement it effectively, and how Data Sleek helps enterprises unlock the full potential of this feature.
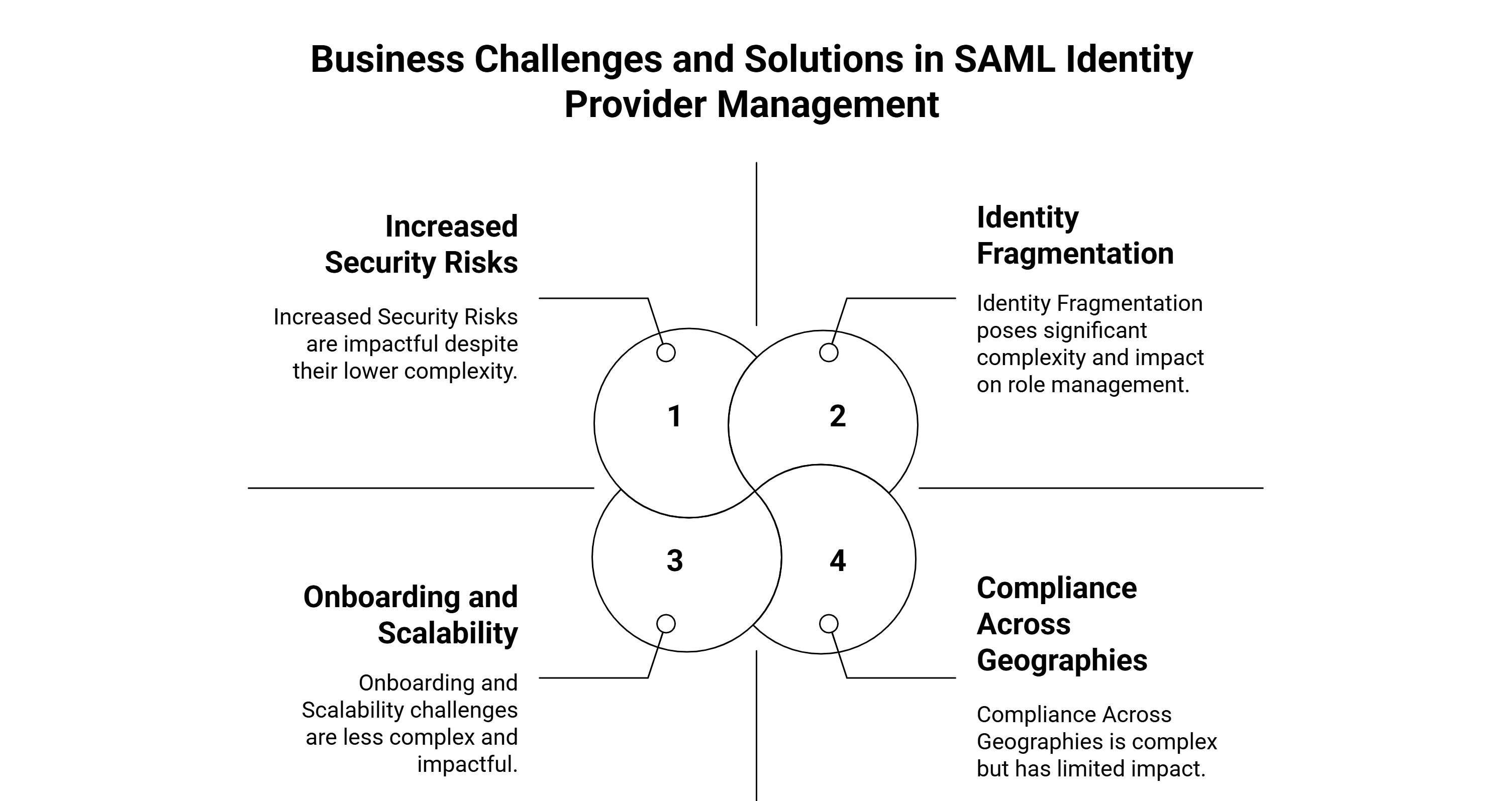
What Are the Key Business Challenges of Using Multiple SAML Identity Providers in One Amazon Connect Instance, and How Can You Solve Them?
While the new feature is powerful, enterprises should be aware of the potential roadblocks:
1. Challenge: Identity Fragmentation Across Business Units
- Problem: A global enterprise might use Okta for corporate employees, Azure AD for IT contractors, and Ping Identity for partner access. Without a unified approach, this leads to complexity in role management and policy enforcement.
- Solution: Configure attribute-based access control (ABAC) to map attributes (like department, role, or location) consistently across IdPs. This ensures agents, supervisors, and external users get the right permissions, no matter which IdP they log in from.
2. Challenge: Increased Security Risks with Multiple IdPs
- Problem: More identity providers mean more entry points for potential breaches if not managed properly.
- Solution: Use AWS IAM Identity Center with conditional access policies. According to a 2025 Gartner report, companies that adopt centralized IAM enforcement reduce identity-related incidents by 42% compared to those with decentralized access.
3. Challenge: Onboarding and Scalability
- Problem: Large enterprises with seasonal workers or BPO partnerships need quick provisioning, but manual setups slow down operations.
- Solution: Automate onboarding with SCIM (System for Cross-domain Identity Management). This allows bulk user sync from each IdP into Amazon Connect roles with minimal admin effort.
4. Challenge: Compliance Across Geographies
- Problem: Multinationals must meet different compliance requirements (GDPR in Europe, HIPAA in the US, DPDP in India as of July 2025).
- Solution: Enable audit logging across all IdPs with AWS CloudTrail and integrate with SIEM tools like Splunk for full visibility.
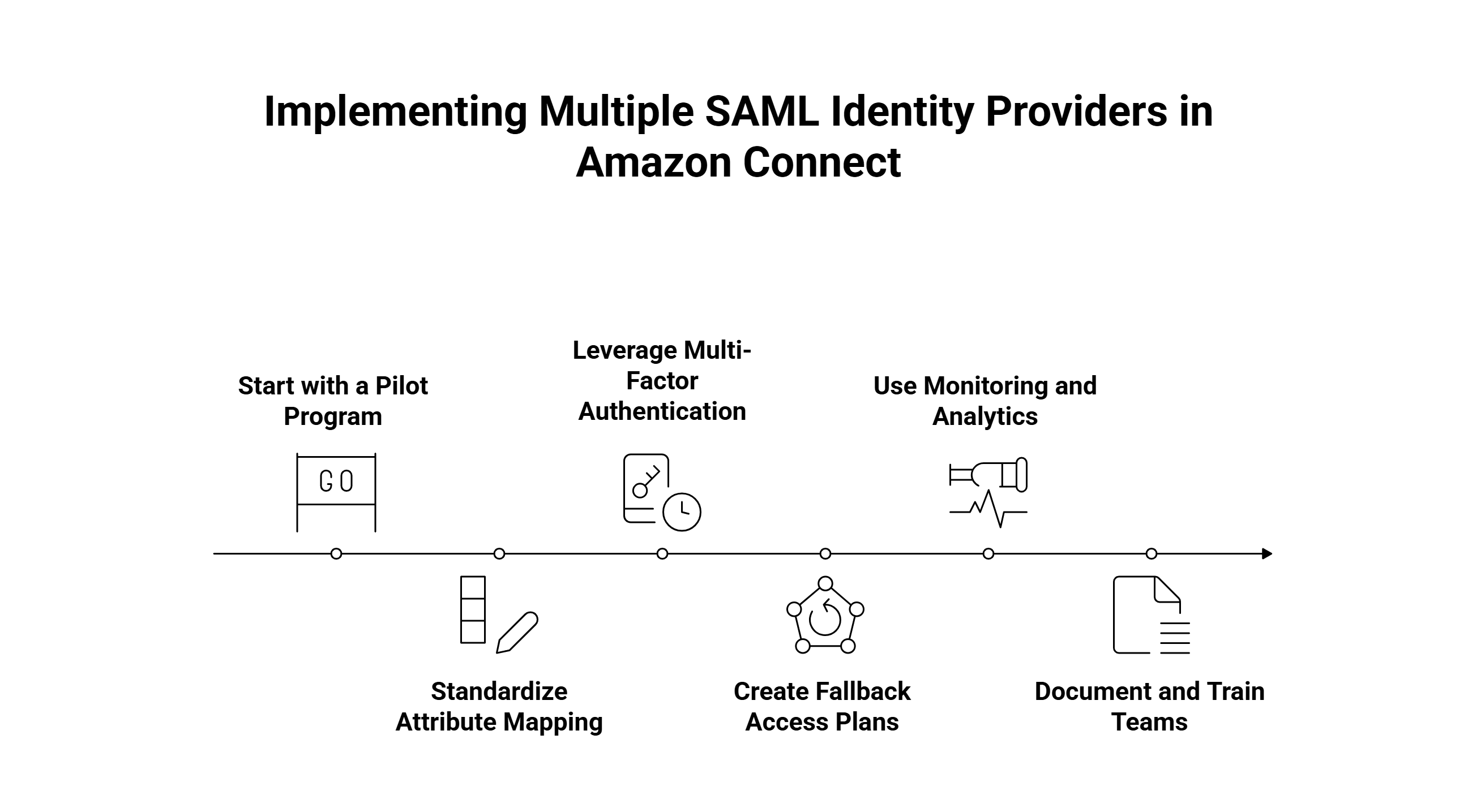
What Are the Best Practices for Implementing Multiple SAML Identity Providers in Amazon Connect Without Disrupting Operations?
Implementation requires careful planning. Here are best practices tailored for 2025:
Start with a Pilot Program
Roll out multiple IdPs for a single department first. Measure login success rates and agent productivity before scaling across the organization.
Standardize Attribute Mapping
Define a global schema (e.g., “department,” “role,” “location”) that applies across all IdPs. This prevents role confusion when users authenticate through different providers.
Leverage Multi-Factor Authentication (MFA)
Even with multiple IdPs, enforce MFA across the board. A recent IBM Security study (2025) found MFA adoption reduces account takeover incidents by 99.2%.
Create Fallback Access Plans
In case one IdP experiences downtime, establish a fallback mechanism. For example, route users through AWS IAM Identity Center temporarily.
Use Monitoring and Analytics
Monitor login events across all IdPs. Amazon CloudWatch dashboards now provide unified visibility for SAML authentications as of 2025 updates, making it easier to spot anomalies.
Document and Train Teams
Ensure your IT, compliance, and customer support teams understand how different IdPs interact with Amazon Connect roles. Training reduces misconfigurations.
How Does Data Sleek Help Enterprises Succeed with Multiple SAML Identity Providers in Amazon Connect?
At Data Sleek, we specialize in helping enterprises go beyond “just setting it up.” Here’s how we add value:
Custom Integration with Enterprise Systems
For a retail client in 2025, we integrated Amazon Connect with both Okta and Azure AD while syncing roles into Salesforce CRM. The result? A 35% faster onboarding time for seasonal agents.
End-to-End Security Framework
We design IAM policies and MFA enforcement tailored to industries like banking, healthcare, and retail, ensuring compliance with GDPR, HIPAA, and India’s DPDP Act 2025.
Performance Monitoring & Analytics
We build custom dashboards that allow CX leaders to monitor login metrics, identity-based performance, and security compliance in real time.
Scalable Architecture
Instead of one-size-fits-all, we architect solutions that can handle thousands of simultaneous logins across multiple IdPs without downtime.
Example: For a BPO client managing agents across three continents, we helped implement four SAML IdPs in one Amazon Connect instance. This reduced operational silos and improved CSAT scores by 18% within the first quarter.
Comparison: Traditional Single IdP vs. Multiple IdPs in Amazon Connect (2025)
| Factor | Single IdP Setup | Multiple IdP Setup (2025) |
|---|---|---|
| User Management | Centralized, but rigid | Flexible, supports multiple orgs |
| Security | Limited to one IdP’s policy | Centralized IAM with multi-IdP policies |
| Onboarding Speed | Slower for diverse users | Faster with SCIM automation |
| Compliance | Harder for multinationals | Easier with per-IdP audit logs |
| Scalability | Limited | Enterprise-ready with thousands of users |
Conclusion: The Future of Identity Management in Amazon Connect
The ability to use multiple SAML identity providers in a single Amazon Connect instance is a game-changer. Enterprises no longer need to choose between flexibility and security—they can have both.
By following best practices, addressing challenges head-on, and partnering with experts like Data Sleek, organizations can build a secure, scalable, and future-ready contact center that empowers both agents and customers.
Ready to integrate multiple SAML IdPs into your Amazon Connect environment?
Contact Data Sleek today to ensure your setup is not just functional, but optimized for performance, compliance, and long-term growth.
FAQs on Using Multiple SAML Identity Providers in Amazon Connect
Q1. Can I use Okta, Azure AD, and Ping Identity together in one Amazon Connect instance?
Yes. As of 2025, Amazon Connect fully supports multiple SAML IdPs, allowing you to configure each provider for specific user groups.
Q2. How does this impact compliance requirements like GDPR or DPDP (India 2025)?
Using multiple IdPs actually makes compliance easier. Each IdP can enforce local data regulations while still connecting to a centralized Amazon Connect environment.
Q3. Does supporting multiple IdPs slow down login performance?
No. With attribute-based access control and SCIM automation, login times remain consistent—even at enterprise scale.
Q4. Is this feature secure enough for financial services?
Absolutely. With MFA, centralized IAM, and CloudTrail logging, enterprises in banking and fintech can maintain regulatory compliance while enabling multi-IdP access.
Q5. Why should I work with Data Sleek for implementation?
Because we don’t just integrate multiple IdPs—we align them with your CRM, ERP, and compliance workflows. Our hands-on expertise ensures personalization, security, and measurable ROI.
Q6. Can I use both corporate and partner identity providers in the same Amazon Connect instance?
Yes. Amazon Connect allows you to configure multiple SAML-based IdPs, meaning you can integrate your corporate Active Directory via AWS SSO alongside a partner IdP. This makes it easier to onboard contractors, BPO agents, and third-party teams without merging identity systems.
Q7. How does using multiple SAML IdPs affect compliance and security audits?
Multiple IdPs actually enhance compliance because each user group authenticates through its own trusted provider. You can also apply policies like MFA, session timeouts, and logging separately for each IdP. This ensures granular control and clearer audit trails for regulatory requirements such as HIPAA, PCI, or GDPR.
Q8. Is there an additional AWS cost for configuring multiple SAML Identity Providers?
No, there’s no extra charge for setting up multiple IdPs in Amazon Connect. Costs are based on Connect usage (minutes, messages, etc.) and the IdP service provider you’re using. However, enterprise-scale deployments should plan for potential costs associated with external IdP licensing or API usage.
Q9. How can Data Sleek help optimize multiple IdP setups in Amazon Connect?
At Data Sleek, we don’t just configure the IdPs—we design a robust identity strategy. For one of our clients in the financial sector, we integrated 2 corporate IdPs and a partner IdP with Amazon Connect, reducing onboarding time by 50% and ensuring compliance with SOC 2. We also provide ongoing support for scaling and policy enforcement.